
For any business that collects data from Australian residents subject to the Australian Privacy Act, you don’t want to ignore the specific data breach procedures to follow. The Australian Privacy Act data breach protocols offer strict guidelines your business must follow to avoid potential fines.
While you should take every step to minimize the risk of a breach, you cannot eliminate its risk completely. And if the time ever comes when your data is compromised, you want to be sure you know exactly how to handle the situation and remain compliant.
The good news is we can help you do just that. This article will cover the Australia Privacy Act in detail, the criteria to classify data breaches, a helpful outline of a data breach response plan, and the potential penalties you face for not complying with the Australia Privacy Act.
Let’s dive in.
Key Takeaways
The Australia Privacy Act was created in 1988 but was updated in 2022 to keep up with the growing demand for data protection and privacy in today’s digital landscape. The update gave the Office of the Australian Commissioner authority to enforce the law.
Your business must notify affected consumers and the Office of the Australian Commisioner of breaches identified as eligible data breaches. Eligible data breaches are breaches that could potentially cause consumers “significant harm.”
The Office of the Australian Commissioner requires that your business contain, assess, notify, and review immediately following a breach. Non-compliant businesses can be fined up to AUD 50 million ($32 million).
Australia Privacy Act Explained
Australia Privacy Act Explained.jpg

The Australia Privacy Act is the legislation created by the Australian Government to regulate how businesses protect data privacy and handle consumers’ personal information.
The Privacy Act was initially created in 1988, but to keep up with the changing landscape of digital commerce and the growing need for data protection, the Australian government amended and updated the law in 2022. One of the more significant updates was implementing several data subject rights that businesses must grant to their consumers.
Another notable change was the significant increase in the maximum fines a business could receive for a violation. The Australia Privacy Act created this shift in power and stricter regulations regarding data protection and privacy to protect its consumers and adapt to the growing threat of data breaches.
The Office of the Australian Commissioner enforces the law, with the privacy commissioner holding most of the power in assessing fines to non-compliant businesses.
The Australia Privacy Act applies to the following:
Businesses that operate in Australia or sell to and collect personal information of Australian consumers
Reported annual income of more than AUD 3 million or $2 million
Australian government agencies are automatically included
Even with less than 3 million AUD of income, any business in the healthcare industry that collects consumers’ health data, credit reporting entities, a business that trades in personal information, or is an operator of a residential tenancy database
The Australian Privacy Act has specific principles and guidelines for your business to protect consumers. Your business should research and understand the framework thoroughly to avoid significant penalties and hefty fines.
What is Considered a Data Breach?
What is Considered a Data Breach.jpg

A data breach is defined by the Office of the Australian Information Commissioner as the personal information of a consumer that a business holds being accessed or disclosed without authorization or lost.
It is crucial to receive explicit consent from a consumer before collecting personal information. Your business should always include the possibility of a data breach in your consent form and notify consumers of the risk.
The Office of the Australian Information Commissioner defines personal information as any information about a consumer that has been identified or is identifiable. Even information that does not relate directly to the consumer can be used to identify them when combined with other information and is considered personal information as a result.
A malicious third party, human error within a business, or inadequate data security or information processing systems typically cause data breaches.
Depending on the cause, scale, and type of data, there are differing types of data breaches. Here are some common examples of types of data breaches:
Loss or theft of a device or physical files that contain consumers’ personal information
An employee accesses personal information or data without permission
Unintentional disclosure of personal information due to human error (sending an email to the wrong person)
Disclosure of personal information to a malicious third party by a business because of insufficient identification verification
Out of these types of data breaches, the Australian government requires that your business report any notifiable data breach that could cause serious harm to them and any consumer affected under the privacy law.
Notifiable data breaches are known as eligible data breaches and consist of the following criteria:
A consumer’s personal information is disclosed or accessed without authorization
A consumer’s personal information is lost, and unauthorized access or disclosure is possible
The personal information exposed is likely to cause serious harm to the related consumer
The responsible business has no remedy to prevent the possibility of serious harm
Why Do You Need a Data Breach Response Plan?
Your business must have a data breach response plan in place. A thorough, established plan can help minimize the damage to affected consumers and your business. Below are the biggest reasons why a data breach response plan is essential for your business:
Compliance with Australia Privacy Act
If your business is subject to the requirements of the Australia Privacy Act, you are legally required to take “reasonable steps” to protect consumers’ personal information.
Having a data breach response plan is a sure way to show your commitment to data protection and be considered a reasonable step as part of your corporate compliance.
Damage Control
Another great benefit of a data breach response plan is that quick, decisive action can significantly lower the damage resulting from a breach. Not only can you limit the damage that may result to the related consumer but to your business as well.
Cleaning up after a data breach can be costly. Your business must spend time and money trying to track down and eliminate the personal information that was disclosed. A data breach response plan can minimize these costs and the harm done to consumers.
Preserve Public Trust & Reputation
Finally, an effective data breach response plan can display to consumers your business’s commitment to data privacy and thorough data protection. A data breach can harm your reputation, but handling it effectively and minimizing damage will reflect well in the eyes of the public.
Consumers will be more confident in your business’s ability to protect their information and that you are committed to handling their personal information securely.
Data Breach Notification Response Plan
Data Breach Notification Response Plan.png
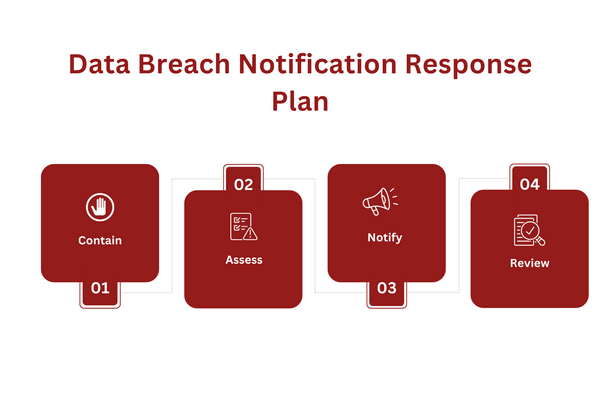
No two data breaches will be the same, and each case will have numerous factors that influence how your business should respond. Your data breach notification response plan should follow these general steps to minimize damage while you react accordingly to the intricacies of each incident.
Contain
The first and most crucial step is how your business acts immediately upon detecting the breach. If you can take any action to prevent further access or disclosure, the sooner, the better. The first steps can include shutting down your systems or changing accessibility.
The Office of the Australian Information Commissioner recommends the following questions to ask yourself to contain the breach as best as possible:
How did the data breach happen?
Is the personal information still being shared or disclosed?
Who can access the personal information?
What are the first steps your business can take to stop this disclosure or access?
If you can identify the data breach as an eligible data breach, it is your business’s responsibility to notify the related consumer(s) as soon as you can. You are then required to assess the data breach, which we will cover in the next step.
It is crucial for your business not to destroy potential evidence during the containment step. Any information that can help you find out the cause of the breach or help you better react to the potential harm to the consumer should be preserved.
Assess
After taking the initial steps to contain the breach as much as you can, your business should then prioritize assessing the breach. An assessment will include your business gathering as much information as possible about the breach, including how and why it happened, the information involved, and the affected consumers.
By gathering this information, your business can gauge the potential risk to related consumers and the best actions to take. The containment and assessment steps must be carried out as soon as possible.
The information you gather about the breach will allow you to decide if you need to notify the consumer whose personal information was involved. Consider the type of information, the extent of the breach, and the degree of harm that could result to the consumer.
Notify
The next step is deciding whether to notify the affected consumer(s). Notifying should also be considered on a case-by-case basis, as there are instances where it is not the best course of action.
If you notify a consumer about a breach that is not particularly harmful, it could cause them unnecessary stress.
Your business should always consider if you must notify individuals and the Commissioner, any personal processes that include notifications, how you will notify, who you will notify (other than the Commissioner and affected consumers), and if you need to notify other investigation agencies or other entities.
A good data breach response plan will include a notification step that allows you to give individuals a chance to protect their information. Consistent notifications will also allow you to garner consumer trust and show your efforts to protect their data privacy.
You may notify by mail, email, or any other individual way. If that is not possible, making a public statement on the website and taking reasonable steps to publicize it will be required.
Review
The final step is an internal review of:
The initial cause of the breach
Your business’s data security systems/practices
A strategy to prevent similar breaches
Regular auditing to ensure effective implementation of new procedures
Improved employee training
Any other businesses involved in the breach
The review step is primarily to improve your business’s data security and implement systems to prevent breaches in the future. Consider all breaches that have occurred to formulate the most effective prevention method possible.
It is crucial to follow up the review step with thorough data breach prevention. Your business should conduct regular audits and implement practical employee training to be prepared for any future breaches.
You can outsource your compliance needs to us at Captain Compliance to assist your business in creating an effective data breach response plan and future prevention strategies. Our full suite of compliance services includes regular audits and compliance training to strengthen your business’s data security systems.
Penalties for Non-Compliance with the Australian Privacy Act
Under the Australian Privacy Act, the Privacy Commissioner can impose maximum fines of up to AUD 50 million ($32 million) for a violation. In addition, there are separate penalties that are charged for repeated breaches.
These additional fines can include up to 30% of your business’s revenue during the breach or for the previous year, depending on which is longer. For responsible individuals, the fine can be up to AUD 2.5 million ($1.6 million).
In addition to the monetary fines, the Privacy Commissioner also holds the authority to undertake your business’s data security system, make you provide compensation to victims, and disclose the details of the breach and their investigation to the public.
Closing:
The Australian Privacy Act has specific regulations for businesses’ data breach response plans. If your business is subject to the law, you should be aware of how the Office of Australia Information Commissioner defines “eligible data breaches” and the required steps your business must follow to remain compliant.
Our team of compliance professionals can guarantee your business compliance with the Australia Privacy Act. Don’t miss out on our compliance solutions and services that will ensure compliance with the Privacy Act and help your business create an effective data breach response plan.
Get in touch with us to learn how we can help your business with all your data breach response planning and ensure your compliance with the Australian Privacy Act and any other relevant frameworks.
FAQs
What are the consequences of breaching the Privacy Act Australia?
Businesses that violate the Australian Privacy Act can be subject to fines of up to AUD 50 million (32 million dollars). Any individual responsible for a violation can be subject to fines of up to AUD 2.5 million (1.6 million dollars).
Get in touch with us to utilize our compliance services and avoid significant fines!
Who is liable for Data Breach Australia?
Your business is liable for a data breach under the Australian Privacy Act. The responsible individual can also be individually fined under the law. Breaches classified as eligible data breaches also must be reported to the affected consumer and the Office of the Australian Information Commissioner.
Find out about data protection solutions to prevent breaches.
What are the steps for OAIC data breach?
The Office of the Australian Information Commissioner requires your business to contain, assess, notify, and review immediately following a data breach.
Read about the most effective data breach response protocols here!
Who do you report a data breach to Australia?
If the data breach could cause significant harm to a consumer or business, you are required to notify those affected parties as well as the Office of the Australian Information Commissioner.
Learn why consent is so important and the potential consequences of data breaches
What is the purpose of the Australian Privacy Act?
The Australian Privacy Act is meant to protect consumers’ personal information and give them more control over how businesses handle their information.