
Every month there are new data privacy laws being enacted or in discussion. The biggest was right after the 2024 IAPP Conference in Washington, D.C. when they said lets talk about the American Data Privacy Act (ADPA) where a federal law could affect 90,000 businesses that don’t currently require compliance.
2025 will bring new privacy laws in states and a potential Federal law but for now experts from Captain Compliance can help with the ever growing list of new privacy laws.
With an increasing number of businesses dealing with large scales of consumer data, following multiple regional data privacy regulations has become a challenge. This is why businesses are shifting towards a holistic approach to creating a data privacy strategy that encompasses different regulatory requirements.
But what is a data privacy strategy, and why is it important?
We’ll cover the basics of what a data privacy strategy is in this article. We’ll also dive deeper into how to create an effective privacy strategy and the best practices to consider when doing so.
Let’s get started!
Key Takeaways
A privacy strategy is crucial for businesses to manage and protect sensitive data, ensure compliance with regulations, and prevent reputational damage.
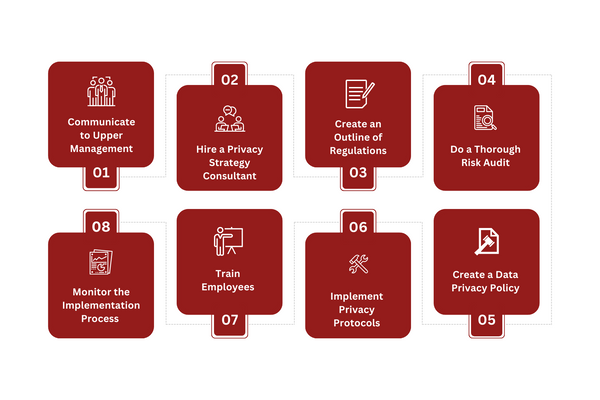
Creating a privacy strategy involves communicating its importance to upper management, hiring a privacy consultant if necessary, conducting risk audits, drafting internal policies and action plans, and more.
Best practices for creating a successful privacy strategy include prioritizing user consent, implementing robust security protocols, and ensuring overall compliance with external regulations through regular auditing schedules
What is a Privacy Strategy?

A privacy strategy is a set of rules and processes designed to help businesses manage and protect sensitive data. A data privacy strategy includes a vision of the business with regard to data privacy and practical steps to help with data protection.
Privacy strategies are usually designed for businesses that work in several regions, each with different data privacy regulations.
For example, a corporation that provides services to Californians will have to follow the CPRA. However, if they provide services to consumers in the European Union, they will have to be GDPR compliant as well. In such scenarios, having a privacy strategy encompassing various legislative requirements is helpful.
Why is it Important to Have a Privacy Strategy?
As discussed above, having a privacy strategy can help ensure compliance with various regulations.
But why is this important?
For one, it protects you from getting penalties due to non-compliance. More importantly, it helps businesses protect their internal systems and sensitive data, which could prevent a loss of reputation.
With the right approach, a well-designed privacy strategy can help ensure internal and external data protection, prevent data leakage, and reduce the risks of dealing with sensitive data.
How to Make a Privacy Strategy
Even though the importance of a privacy strategy is clear to most businesses, few put the time into creating one. This results in unintentional data leaks, which cost businesses millions of dollars yearly.
Fortunately, creating a privacy strategy isn’t rocket science, and with the right tools and personnel, it can easily be implemented in any organization.
Here are some steps to help you create a privacy strategy for your business, regardless of its size or industry:
1. Communicate the Importance of a Privacy Strategy to Upper Management
The primary reason why most businesses fail when trying to create a privacy strategy is because upper management doesn’t buy into the process. It’s the same reason why 90% of all data breaches are caused by human error.
Fortunately, getting upper management to support creating a privacy strategy has become easier, with data privacy regulations becoming stricter.
Furthermore, the hefty fines imposed by regulators for non-compliance are enough motivation for upper management to get serious about data privacy.
2. Hire a Privacy Strategy Consultant
Creating a privacy strategy for someone who isn’t an expert can be challenging. You’ll have to understand the technical jargon used in privacy policies and know which privacy regulations apply to your business, among other things.
This is where a privacy consultant comes in.
They will conduct an audit of your business’s current privacy processes, identify possible risks, and help create clear data privacy and security protocols.
Privacy consultants are also there to ensure your business implements corporate compliance procedures and that your privacy strategy is in line with global data privacy regulations.
3. Create an Outline of the Privacy Regulations Your Business Falls Under
Once you hire a data privacy consultant, they’ll make an outline of the relevant regulations your business falls under. This will vary based on your industry, scope of operations, and how you manage and collect data.
However, it’s crucial not to leave out any privacy regulations when creating a privacy policy. It’s also helpful to consider the guidelines of the proposed Global Privacy Control standard, especially if you operate globally.
4. Do a Thorough Risk Audit
Once you have an overview of which data privacy regulations your business falls under, you’ll need to conduct a risk audit. Risk audits should preferably be conducted by a data privacy consultant or external compliance services provider.
This will give you a good idea of where your business stands in terms of data privacy and will highlight areas for improvement.
5. Create a Data Privacy Policy and Action Plan
The next step in creating a privacy strategy is to draft internal privacy policies and an action plan for implementing them.
A privacy policy will usually cover the following:
How information is collected
What the business uses data for
User rights and responsibilities
Security protocols for processing data
Other information related to how data is used and accessed
Once you have a privacy policy, you can easily create an action plan that implements its core principles.
6. Implement Data Security and Privacy Protocols
To ensure your privacy strategy has an impact on the business, you’ll need to implement relevant security protocols. These protocols prevent the misuse of data and are key to reducing the risk of data breaches.
Security protocols could include:
Restricting and monitoring log access
Encrypting sensitive data
Ensuring two-factor authentication for data access
Creating a system for security audits
When implementing these security protocols, it helps to follow relevant cybersecurity frameworks such as the NIST framework or PCI DSS.
7. Train Employees Based on the Privacy Strategy Framework
Your privacy strategy is bound to fail if employees aren’t well-versed in the relevant security protocols. When conducting training sessions, always ensure that data access and other security protocols are well-drilled.
However, training is useless without effective support systems.
There’s no use in training employees on data safety if the business hasn’t implemented rules for data encryption or if security software is outdated.
8. Monitor the Implementation Process to Ensure Compliance
Lastly, you’ll need to monitor the whole process and conduct regular security audits to ensure internal compliance. This is usually the job of a compliance officer, and external audits are more effective in assessing real risk.
Once risks are identified, you can redo the process and patch up any shortcomings in line with the privacy strategy.
Privacy Strategy Best Practices
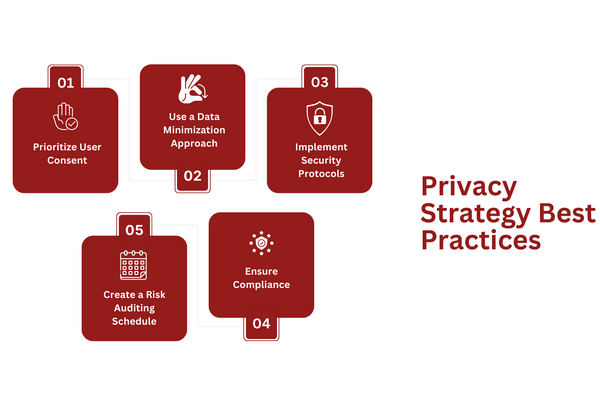
A privacy strategy won’t always guarantee your business is safe from data leakages and external threats. Privacy strategy best practices can help ensure your business’s privacy strategy aligns with data protection principles for the 21st century.
Here are some best practices to follow when creating a privacy strategy:
1. Prioritize User Consent
User consent is a core part of data protection regulations and should be a priority for your privacy strategy too. While many regulations restrict what type of data you can collect, most allow businesses to collect sensitive data with prior consent.
By prioritizing user consent, your business can achieve data security compliance and avoid expensive lawsuits.
2. Use a Data Minimization Approach
With so many curbs on what data businesses can collect and how the data should be processed, having a data minimization approach can help.
But what is data minimization, and how does this approach fit in with your privacy strategy?
In simple terms, it means collecting only necessary data and disregarding the rest.
3. Implement Robust Security Protocols
Security protocols are essential to prevent data breaches caused by internal and external failures. These include password strength requirements for employees, two-factor authentication, and updating anti-malware software.
If your business experiences a data breach because of a lacking of these basic protocols, the penalties can be severe.
4. Ensure Compliance With External Regulations
While every business will fine-tune its privacy strategy according to its specific requirements, you can’t ignore external regulations.
Always design a comprehensive privacy strategy that covers both internal requirements and external regulations.
5. Create a Risk Auditing Schedule
Another best practice for creating a privacy strategy is to create a risk auditing schedule. These audits should be conducted regularly and help identify possible data risks.
While many businesses conduct yearly risk audits, it’s best to conduct them more regularly to prevent accidental breaches.
Closing
A privacy strategy is the backbone of your business’s internal privacy processes. However, it’s a core part of ensuring data compliance.
This is where Captain Compliance comes in.
Our compliance solutions include designing your business’s privacy strategy, drafting privacy controls, and conducting thorough privacy audits to ensure total corporate compliance. We can ensure your business has complete compliance without you having to worry about it again. Get in touch today!
FAQS
What Does a Privacy Strategy Consist Of?
A privacy strategy consists of rules, policies, and procedures outlining the privacy principles of an organization. It also consists of data privacy standards that have to be implemented in further processes.
Learn more about the GDPR privacy principles
What is Control Privacy Design Strategy?
The control privacy design strategy is a strategy used to implement data privacy controls into systems, procedures, and protocols. It emphasizes data minimization, user consent, and transparency.
Learn more about cookie consent
What are the 5 Dimensions of Privacy?
The 5 dimensions of privacy include people, projects, data, settings, and output. These are used to categorize the privacy risk an organization faces.
Contact us today for superior compliance
Who is Responsible for Creating a Privacy Strategy?
A compliance officer or data privacy officer is responsible for creating the privacy strategy for any business. They are experts in data privacy laws and understand how to implement security protocols for data protection.
Learn more about the best data privacy consultancy
What are the 6 Core Privacy Principles?
The 6 core privacy principles are lawfulness, fairness, transparency, and limitations on data collection, processing, and storage.
For help developing a compliant privacy strategy you can connect with a compliance superhero today at Captain Compliance.